Hi, I’m MICHAEL MUYAMBANGO
ICTs-4-health & INFORMATICS expert
About Me
Michael Muyambango
Happy Clients
Projects Completed
Working Hours
CONSULTANCE Services
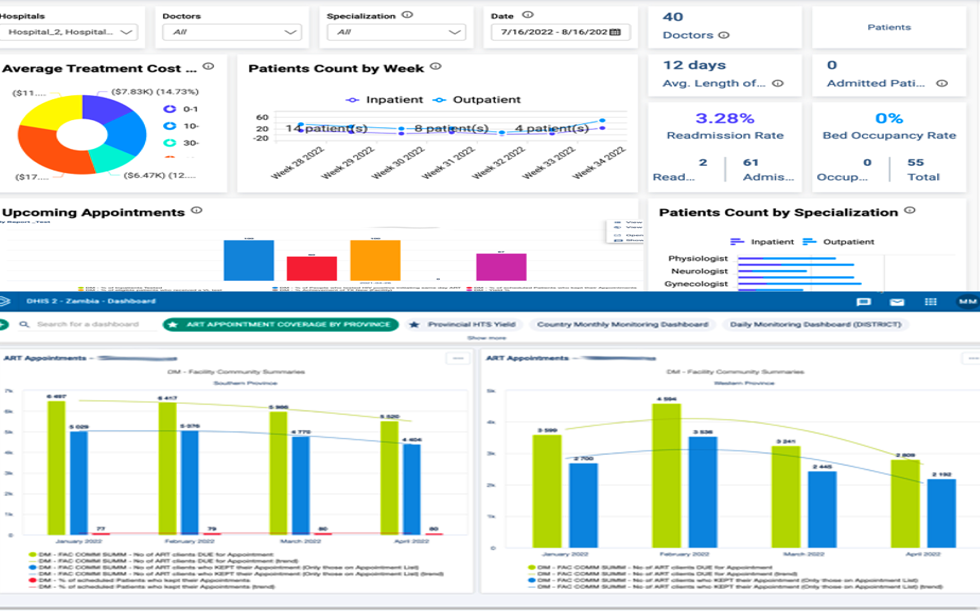
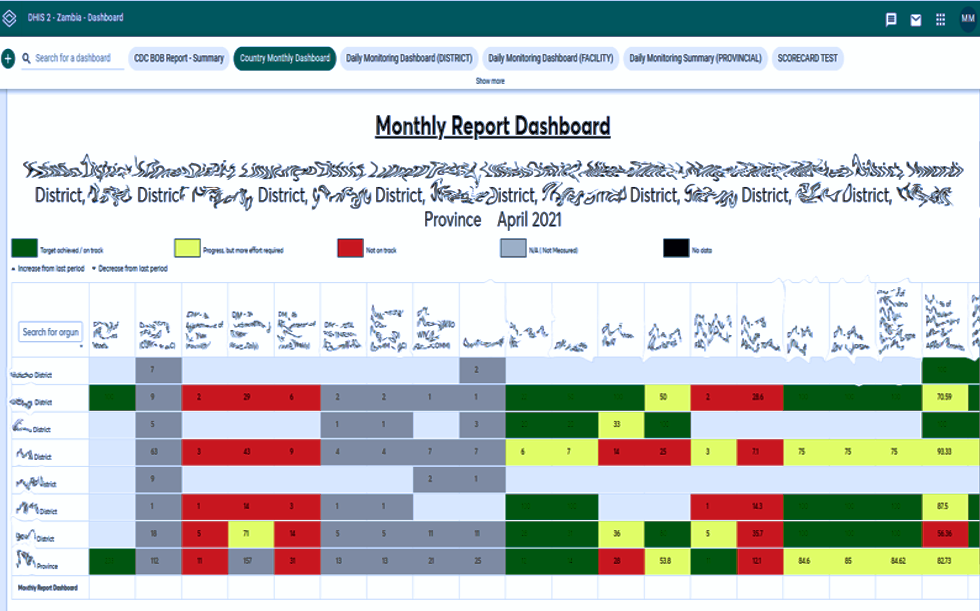
Informatics
- MS ACCESS, SQL
- DHIS 2, DATIM, NEO4J
Systems & Network Administration
- MS Server, LINUX, ACTIVE DIRECTORY, POWERSHELL
- CISCO NETWORKING
Analytics
- SPSS, STATA, R, EPI Info, SAS, NEO4J
- POWER Bi, Tableau, Power Query
Project Management
- SOFTWARE DEVELOPMENT, NETWORKING, COMPUTER REPAIRS & SERVICING
- WEB APPLICATIONS, WEBSITES
My Experience
World Health Organization
Study Data Manager
Jun – Oct 2022
To provide strategic and technical guidance, development & maintenance of the Study Information System & to perform inferential statistical data analytics.
Equal To The Task Zambia
Founder/ Chief Executive Officer
2021 –2022
Providing strategic organization leadership & direction for the plight of people living with disabilities (PLWDs).
ICAP Zambia
Advisor -Informatics
2020 – 2021
Providing informatics technical assistance & support on the HIV Care and Treatment project.
PATH Zambia
Data Associate
2019 – 2020
Health Management Information System Administration and data management.
Zenith Marketing Inc.
Director – IT/Digital Marketing
2016 – 2019
Providing strategic management and leadership including evaluation of all digital marketing activities.
U.S Embassy | CDC Zambia
Foreign National Student Intern
2015 – 2016
Under CDC Informatics Branch to support software development, systems administration & knowledge management.
IIA Zambia
Administrator
Jan – Aug 2015
Management of the Institute’s administration including ICTs.
Care Technology Zambia
Lead ICT Operations
2010 – 2014
Providing strategic management and leadership for ICTs in the organization for optimal service delivery.
Trade-Links Logistics
ICT/Data Analyst
2009 – 2010
Provision of helpdesk support and business insights and analysis.
What My Clients / Colleagues Say
My Portfolio
Latest Blog
Misinformation & Disinformation Associated with mRNA Covid 19 Vaccine Uptakers
INTRODUCTION This article is not to ridicule or question science; rather, to capture various opinions and discuss misinformation & disinformation Associated with mRNA covid-19 vaccines uptakers OR with respect there of. It also discusses viewpoints of what...
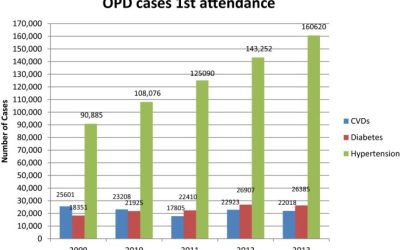
The Health System in Zambia
The Zambian Health System Health is an essential part of life, and one which the Zambian population is facing a severe challenge in. Despite having some of the world’s best natural resources, Zambia still has a long way to go when it comes to providing its population...
Estimating Prevalence of Metabolic Syndrome in Patients With Covid19: Meta Analysis
Background Metabolic syndrome (MS) and COVID-19 appear to be associated with some shared factors that include insulin resistance, abnormalities in lipid metabolism and obesity. Unfortunately, there are limited studies, particularly in sub-Saharan Africa, that have...